Blog
Filters
64 results
-
URL shorteners
Widespread use of instant messaging tools, microblogging services and other social media with character limitation functions has led to a generalisation of shortened links (URLs) to share web addresses. However, when we click on a short URL we cannot be sure of where it will point to, and this may...
Read more
-
Data Governance and Data Protection Policy
Data have become a key factor for any organisation. The skill to process data to build value is a fundamental element of increasing the efficacy and efficiency of the decision making process. Data governance is the strategy for the correct administration and management of data policy in the...
Read more
-
Group Privacy
The concept of privacy is often limited to the sphere of the individual, since it is the dimension most addressed by the regulations. However, most persons are not subject to processing as individuals but as members of specific groups, where groups are the focus of interest. The concept of group...
Read more
-
Privacy risks when logging in other applications with social media accounts
When we install a new app on our mobile device or access a service on a website for the first time we often have to create a user account in order to do so. As an alternative, more services are increasingly offering the possibility of registering using our Google, Apple, Instagram, TikTok, Twitter...
Read more
-
Encryption and Privacy IV: Zero-knowledge proofs
Zero-knowledge proofs (ZKPs) are a set of techniques that allow the implementation of two measures established in Article 25 of the GDPR: minimisation and limitation of data accessibility. The particularity of ZKPs is that they allow assess the certainty of an information without that information...
Read more
-
Blockchain (II): Basic concepts
Blockchain is a distributed information storage technique, without centralized management. This technique makes use of consensus policies to validate the information included and makes use of policies to obtain the integrity of the recorded data.
Read more
-
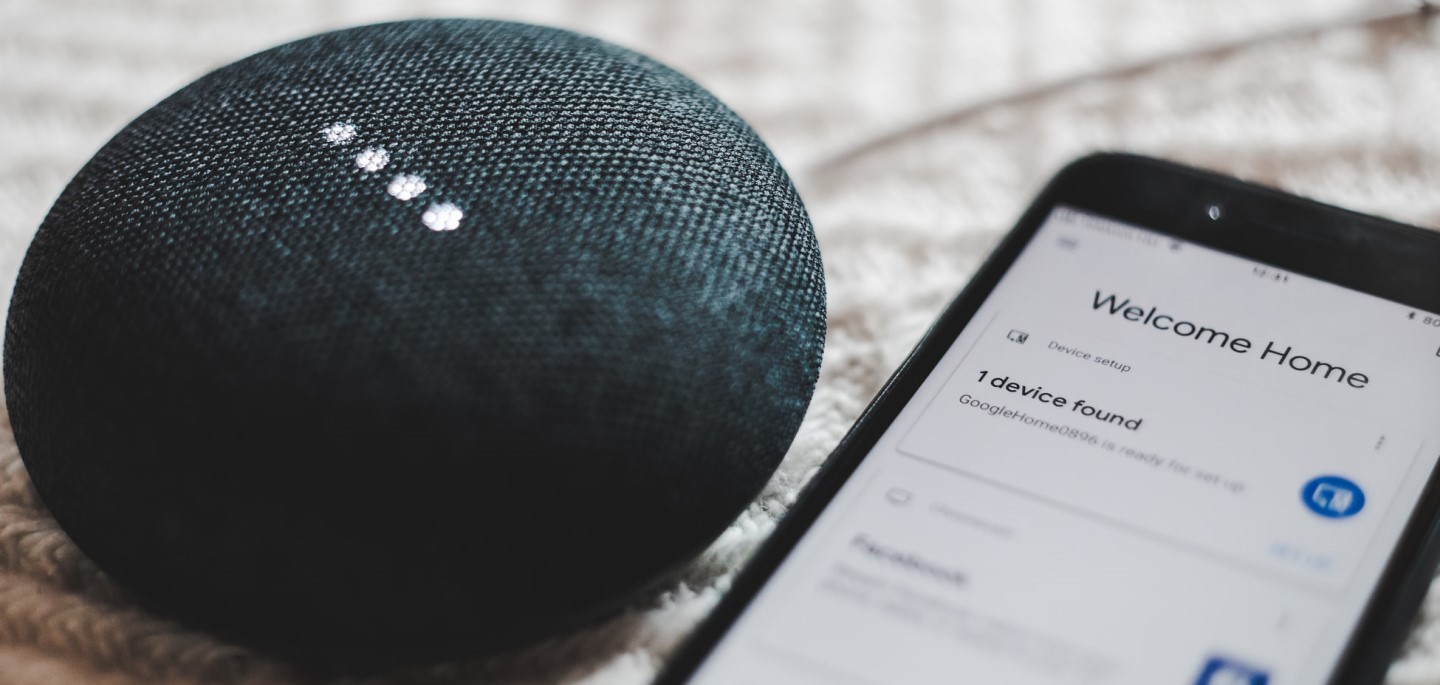
IoT (I): What is IoT and which risks does it entail
Vehicles, toys, watches, kitchen robots, bracelets, heart rate and blood pressure meters, robotic vacuum cleaners, loudspeakers and televisions are only a few examples of connected devices which we have assumed as “normal” in just over a few years, simply by adding the adjective “smart”. This is the...
Read more
-
Personal data breaches: Ransomware and risk management
Ransomware is a cyber-threat with a high impact on personal data that is well known and increasingly common. Within the context of COVID-19, this type of attack is significantly affecting the processing of health-related data. Data controllers must implement specific measures, both of a preventive...
Read more
-
Identification in online payment services
The electronic payments have been evolving considerably, with its use expanding due to the impact of the measures adopted with regard to the coronavirus pandemic. Some of the risks for data protection may arise out of methods to authenticate the identity of the payer and the vulnerability of mobile...
Read more